Network Mapping
Network administrators, ethical hackers, malicious hackers, security auditors and others may need to run network scans to produce network maps. Nmap is a popular network mapping tool. Every day, millions of network scans are run on the internet, but that does not always mean that they are legal. Generally speaking, you should have permission before scanning somebody's network. In this chapter, you will scan a site that explicitly grants permission to scan--scanme.nmap.org.
Learning Objectives
You should be able to:
- Describe the purpose of network scanning
- Run
nmapfrom the command line - Change scanning options
Video Walkthrough
Use this video to follow along with the steps in this lab.
Network Mapping
Network mapping is used to help us understand networks. Network mapping can be used to tell us what computers exist on a network, their IP addresses, and the services that they are running. For example, a server might host websites at the IP address 192.168.10.5. A different server might host email at 192.168.10.25. Nmap is the most popular network scanning software.
Network scanning is kind of like walking around a neighborhood and seeing what houses exist. Each house has a unique address. But you're not sure what is inside each house. So you walk up to each house and check to see if the doors are locked, the windows are shut, and if the hose is turned on. Even if you do not plan to break into the house, the occupants might be concerned about a stranger checking everything out and call the police. Network scanning is a bit like this. With network scanning, you do a little bit of poking around to see what exists on a remote server, but you are not trying to break in.
So is network scanning legal? There is some gray area. It is very rare for somebody to be prosecuted simply for network scanning, but it happens. Generally, networking professionals do not freak out about their networks being scanned--it happens thousands of times per hour. But network professionals do not create the laws, and some prosecutors have applied hacking laws to people who perform network scans. The following is not legal advice, but likely sound advice. Do not do intrusive scans on government sites, especially the CIA, FBI, or Department of Defense. Stay away from banks. Generally, public tech companies like Microsoft, Google, and Amazon will not give you a headache if you scan their publicly accessible networks. The site http://scanme.nmap.org gives explicit permission to perform periodic scans. Be aware that any scans you run can be traced back to you.
Basic nmap scan
- Connect to your Linux terminal.
- Run the following command to do a basic network scan with
nmap. The scan should take less than 30 seconds to complete.
nmap scanme.nmap.org
- If your system does not have
nmapinstalled, install it the way you would install other software.
sudo apt update
sudo apt install nmap
- The output of
nmap scanme.nmap.orgshould look similar to the following.
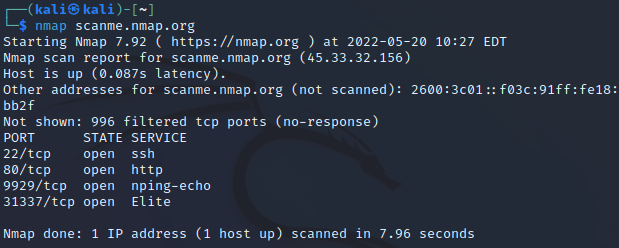
- Running a basic scan is easy. Interpreting the results takes more effort. Your scan results may differ from the scan when the screenshot above was taken. But below is an analysis of what the scan results in the screenshot say.
- The IPv4 address for scanme.nmap.org is
45.33.32.156. - The IPv6 address for scanme.nmap.org is
2600:3c01::f03c:91ff:fe18:bb2f. - The server is running the secure shell (SSH) service, which means that somebody with the right credentials can log on remotely.
- The server is listening on port 80, so a website can likely be reached. Below is a screenshot of the website.
- It is strange for a server to be listening on a very high port--31337. That is the hacker spelling of "elite." The server administrator is probably just having fun with us.
Custom nmap scans
Nmap is powerful. Options can be configured to do things like operating system detection and service version detection.
- In the terminal, run:
nmap -A scanme.nmap.org
- The
-Aparameter tellsnmapto try to figure out the name and version of everything it finds on the server. - Review the output. It should be similar to the following.
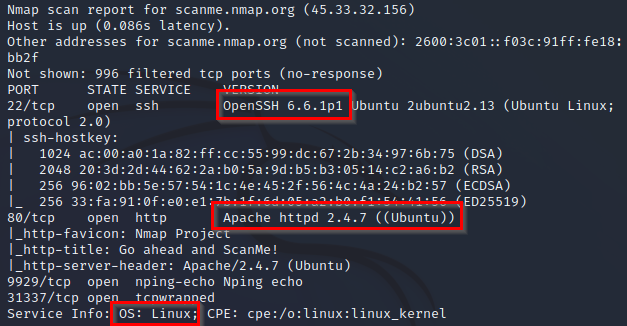
- Note the following.
- For SSH, the server is running OpenSSH 6.6.1p1.
- For the website, the server is running Apache 2.4.7.
- The server's operating system is Linux.
- Run
man nmapin the terminal to see what other options are available.- Find additional options that could be helpful. For example, you might simply try operating system detection with
-O. - Press
qto quit the manual.
- Find additional options that could be helpful. For example, you might simply try operating system detection with
nmap -O scanme.nmap.org
But running this command requires administrative privileges. Run it again with sudo.
sudo nmap -O scanme.nmap.org
If the scan fails, press control+c to cancel the scan.
- What would the following scan options do? Use the manual or a search engine as needed.
-A-O-sS-sU-sn
Reflection
- How would you use network scanning responsibly?
- Imagine you are a network administrator for a company. How would you feel if somebody scanned your network one time? How would you feel if somebody scanned your network 1,000 times?
- How would malicious hackers use
nmap? - How would system auditors use
nmap?
Key Terms
- Network Mapping: The process of discovering and documenting the devices, connections, and topology of a computer network. Network mapping helps in understanding the structure and layout of the network, identifying active devices, and visualizing the relationships between them. It is essential for network management, troubleshooting, and security assessments.
- nmap: Short for "Network Mapper," nmap is a powerful open-source tool used for network discovery and security auditing. It can perform various tasks such as host discovery, port scanning, service detection, and vulnerability scanning. Nmap is widely used by network administrators and security professionals to assess network security and manage network inventory.
- Port Scanning: The process of systematically scanning a computer or network device to identify open ports and the services running on them. Port scanning helps in detecting potential entry points for attackers, assessing the security of networked systems, and ensuring that only necessary services are exposed. Tools like nmap are commonly used for port scanning.